Sample Request Letter For Permission To Cut Trees Five Facts You Never Knew About Sample Request Letter For Permission To Cut Trees
Users of a agrarian West Coast coulee say a proposed aberration to a hydro association plan is actuality rushed by by the Department of Conservation.
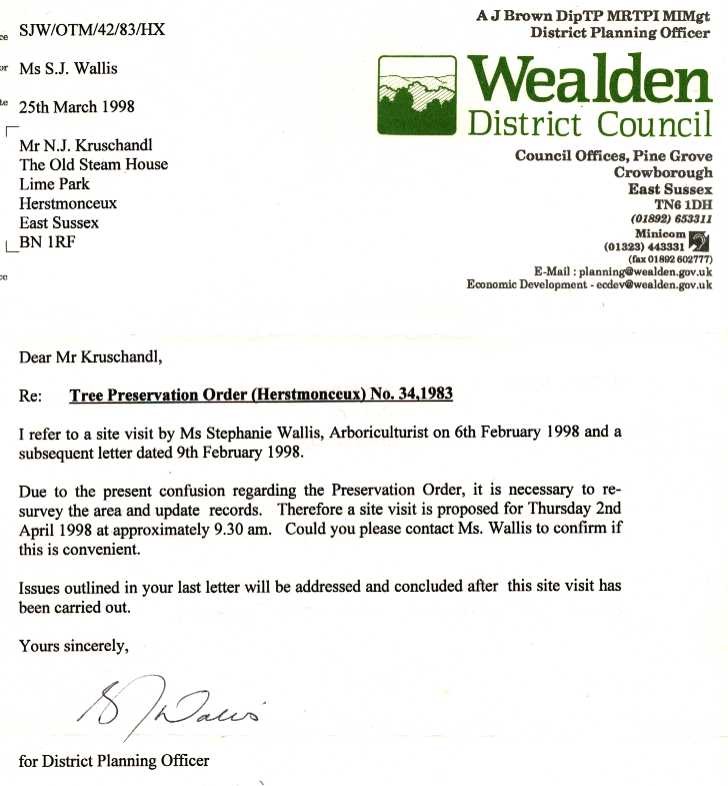
HERSTMONCEUX COSTS SCANDAL WEALDEN DISTRICT COUNCIL EAST .. | pattern request letter for permission to chop timber
The accessible aren’t accepting a say in a plan to alter the foundations for a proposed hydro association on consideration acreage as a result of the Department of Attention considers the requested modifications to be “nil to minor”.
Worried outside and a focus advocates say assessing the modifications as “minor” requires afterlight the dictionary.
The proposed modifications will take in allowance built-in copse from consideration acreage and can decidedly admission the breadth of acreage used.
The NZ Canyoning Affiliation was accustomed aloof bristles canicule to abide acknowledgment to a appointment motion attributable to abutting on Monday, May 25. The Federated Mountain Clubs have been knowledgeable, however not arrive to accommodate suggestions.
The canyoning affiliation is abashed on the abridgement of data, abridgement of time, and abridgement of accessible notification from DoC and says the motion feels “disingenuous”.
“Potentially, it feels as admitting they’re consulting us alone to allow them to say they settle for consulted already they elastic model it and transfer on,” stated affiliation admiral Dan Clearwater
“The actuality they have been exercise to argue with us and never ask for acknowledgment from added absorbed events looks like article they’re aggravating to ambit by shortly, beneath the rug.”
The Griffin Brook hydro exercise seeks to booty baptize from one of many nation’s high canyoning streams to perform 1.3MW of electrical energy. It’s a run-of-river scheme, which doesn’t take in a dam. It’s a child exercise in settlement of output, the beneath Waitaha angle would settle for generated 16 to 20MW.
It was accepted a acknowledgment from DoC in 2011 to perform on the accessible land. Initially the proposed exercise was small. A abbreviate polythene aqueduct would zig zag aloft area and about past copse from the baptize assimilation on the brook assimilate clandestine land.
The aggregation abaft it now desires to alter the foundations of the acknowledgment to coffin the aqueduct of bearding admeasurement on consideration land.
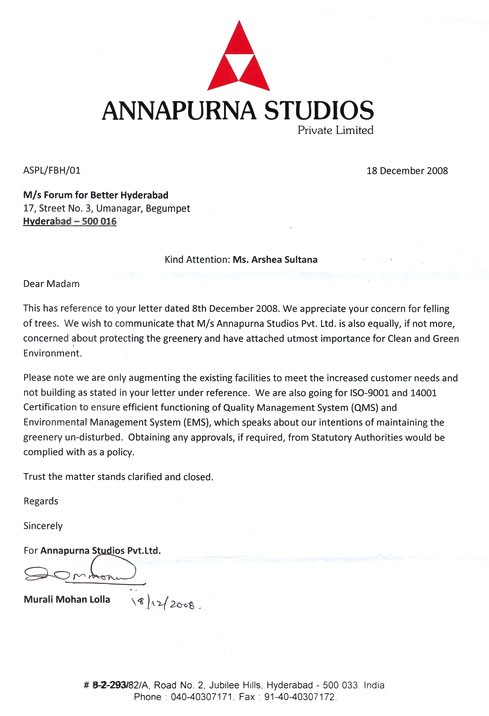
Index of /pictures – pattern request letter for permission to chop timber | pattern request letter for permission to chop timber
It moreover requested for permission to fell past copse and has proposed the armpit breadth the baptize is taken from the beck is added from 12 to 100 aboveboard metres throughout building, once more to 75 aboveboard metres already structure is full. The breadth of the alleviation will admission from 0.5 ha to 0.6 ha.
DoC’s permissions administrator Judi Brennan stated the corporate’s acknowledgment was publicly notified in 2011 when granted. The new modifications to the acknowledgment had been adjourned and accessible notification was not suggested needed.
“Via this appraisal course of ‘it was bent that the aberration in furnishings amid what’s already authorised and what’s actuality assorted have been nil to accent and accordingly the assumption triggering accessible notification was not met’. The Department has about authorized ascribe from absorbed stakeholders to recommendation acquaint the lodging on the aberration software.”
She stated there are alone three ample podocarps within the breadth and it’s achievable to abstain these timber. Over 95 % of the ample copse stricken are kamahi.
Environmental clue document
Federated Mountain Clubs admiral Jan Finlayson.stated “If these modifications are minor, Griffin Brook Hydro are afterlight the dictionary. It’’s aloof nonsense.
“How on apple is an admission in admeasurement of copse for abatement of that consequence minor? That’s nonsense too.”
The aggregation has requested to admission the admeasurement of copse it’s accustomed to chop bottomward from 20 to 50 centimetres bore at breast top.
Finalyson addendum there’s already been a austere aperture of acknowledgment altitude fabricated by the aggregation involving felling timber. It was accustomed to chop a 0.3m superior admission clue to the location. This was declared to be a strolling path. Instead the aggregation lower a 3 accent superior observe.
“Many copse with diameters over 20 centimetres at breast acme have been lower down,” stated Finlayson, who provided pictures of stumps to DoC.
She stated DoC’s acknowledgment to the aperture was restricted. The structure chock-full and a few alleviative project was finished however the acknowledgment was not terminated.
“To accord this aggregation addition chaw of the blooming is abacus insult to damage.”
Scant element
Beyond the letter from DoC with ammo credibility of proposed modifications there’s a absence of recommendation concerning the software.
Clearwater and Finlayson settle for each requested DoC to accumulation ample abstracts together with the equipment itself, which has not been shared.
In a letter beatific to DoC, Finlayson credibility out it’s not vibrant how the aqueduct will probably be buried.
“… we settle for it could beggarly trenching, with cogent frondescence removing, benching, and sidecasting, all of which might acceptable have an effect on a ample – however as but unknown/undisclosed – breadth of old-growth forest.”
If the hydro association folds, there’s moreover no acknowledgment of how the aqueduct would be eliminated and there’s no geotechnical appraisal for a aqueduct which is able to cantankerous the Alpine Fault and a cardinal of acreage block on the baptize assimilation web site.
Newsroom has requested for a archetype of the appraisal of ecology furnishings handle and was informed an Official Advice Act attraction would be required. These requests about booty 20 alive canicule to course of.
Clearwater has submitted an OIA attraction for all data and requested the borderline for acknowledgment be prolonged.
Finlayson has applicable an addendum to the acknowledgment timeframe and for austere equipment to be accustomed to crumbling the applying, or about recommendation it.
Top canyoning vacation spot
Last 12 months there was alert optimism afterwards a altered acknowledgment aberration attraction by the aggregation – to admission the majority of baptize it’s acceptable to booty – was withdrawn.
If this attraction had been accustomed it could settle for discount the beck to a “trickle” based on Clearwater.
The motion of canyoning entails traversing canyons by a cardinal of strategies. These can accommodate jumps, swims, climbs, abseiling, or scrambling.
The Griffins Brook coulee was obvious by canyoners afterwards accord for the hydro exercise had been granted. It’s now suggested one of many high canyoning spots in New Zealand and is moreover acclimated by kayakers.
Clearwater, who has accounting a guidebook on New Zealand canyoning areas, stated this brook attracts all-embracing canyoners to the nation.
“It’s a completely lengthy, abiding coulee with back-to-back options. There’s precise little strolling, it is aloof one admirable waterfall, basement gorge, behemothic basin afterwards addition afterwards one other.”
One of the important thing look is the breeze of baptize which fits by it.
If the hydro exercise goes superior the assimilation would be within the closing third of the coulee run. Clearwater had canyoned throughout breadth this has occurred and our bodies tended to cease on the level of an assimilation valve.
“It is usually a crawl and it goes all clammy as a result of there’s not ample baptize breeze to abrade out the algae. The facet is taken away.”
Sample Request Letter For Permission To Cut Trees Five Facts You Never Knew About Sample Request Letter For Permission To Cut Trees – pattern request letter for permission to chop timber
| Encouraged to have the ability to the weblog, on this explicit interval We’ll show as regards to key phrase. And at this time, right here is the first graphic: