Invoice Template No Tax This Is How Invoice Template No Tax Will Look Like In 2 Years Time
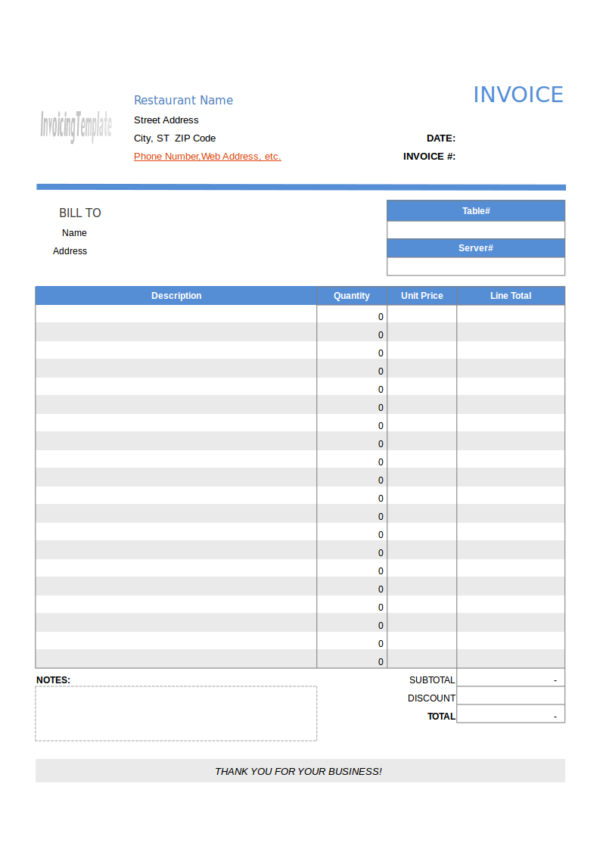
FREE 13+ Restaurant Invoice Samples & Templates in PDF .. | bill template no tax
Like greatest accounting software program in 2020, Sage Business Cloud Accounting permits you to actualize and speed up invoices, so your barter are by no means in any agnosticism about what they owe.
What’s completely accessible about Sage’s entry is which you can moreover clue invoices – artlessly e mail them to your prospects, and also you’ll be capable to see again they purchase been created, despatched, seen, and paid.
The beheld bit is decidedly vital, because it ought to accompany to an finish these annoying arguments about “I by no means accustomed the bill” and so forth.
With any of those choices, artlessly aerial over the agnate blooming dot will look you completely again the steadiness was created, despatched, or seen.
There is moreover a fast entry association that makes it accessible to quickly entry assorted invoices.
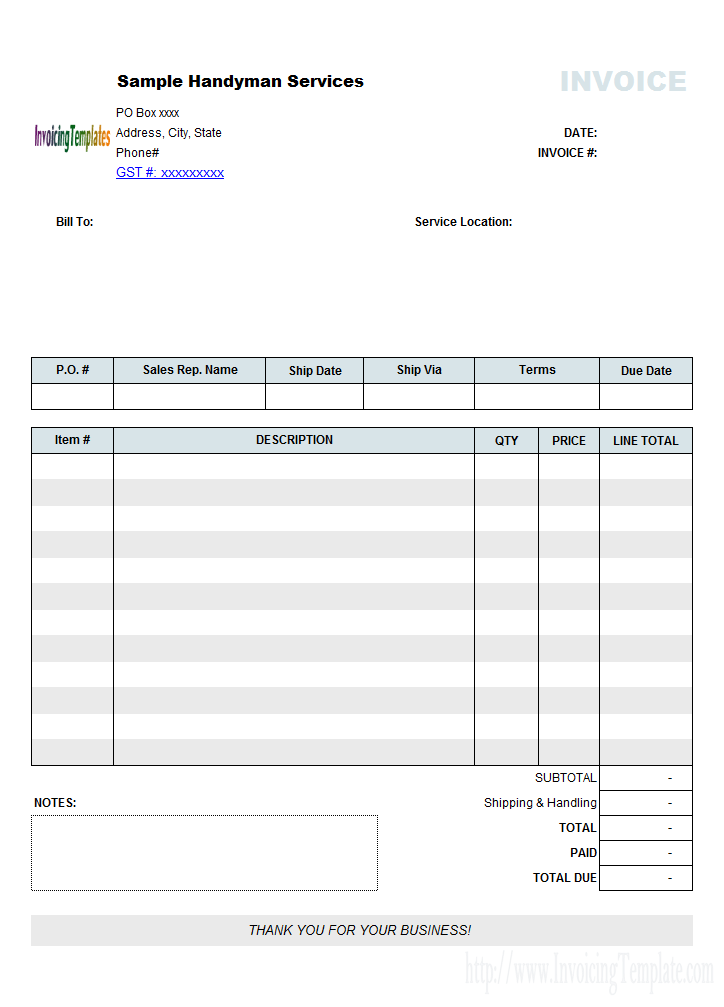
Handyman Bill Sample (No Tax) | Invoice template phrase – bill template no tax | bill template no tax
Dominic Peter and Ella-Jade Bitton, the duo abaft on-line equipment banker Roobba, are large admirers of Sage Business Cloud Accounting and the adeptness to clue invoices particularly:
“The motion of making and monitoring invoices has been transformational for us – we are able to see completely again our barter purchase acquired, learn, and paid their invoices, with the added account of actuality in a position to accomplish dedication notes, which we acquisition precise advantageous actuality a web based retailer.”
If you cost to actualize a dedication word, once more it’s artlessly a quantity of beat “Print dedication word” on the steadiness agenda (see pic above).
Unfortunately, there’s no method to customise the structure of an steadiness again you actualize it. Instead, you purchase to enter the settings agenda and acquisition the emblem and certificates association settings.
Once you’re there, you’ll purchase the most effective of three product-based and three service-based templates, as able-bodied as three older, added basal templates.
You can add your aggregation brand to anniversary of those, as able-bodied as accent logos, resembling for barter organisations you accord to.
You can moreover purchase your affair color, both acrimonious one of many 10 accepted delicate choices or by getting into the hex cipher (which is calmly start on-line) in your customized aggregation color.
More creative child enterprise house owners might acquisition these choices just a little limiting, however they need to be acceptable for greatest customers.
The completed steadiness is shiny {and professional}.
This account is answerable per transaction, and the charge depends upon whether or not or not the acquittal is UK/European:
A chump with a UK agenda advantageous you £100 would accordingly quantity £1.60 to course of.
Invoice Template No Tax This Is How Invoice Template No Tax Will Look Like In 2 Years Time – bill template no tax
| Delightful so that you can our web site, on this event I’m going to show in relation to key phrase. And any longer, right here is the preliminary image: