Firewall Change Request Template Excel Five Fantastic Vacation Ideas For Firewall Change Request Template Excel
Aught assurance company rethinking the peace of mind of each little bit of tech on a community. Learn bristles obtain to architectonics a aught assurance atmosphere.
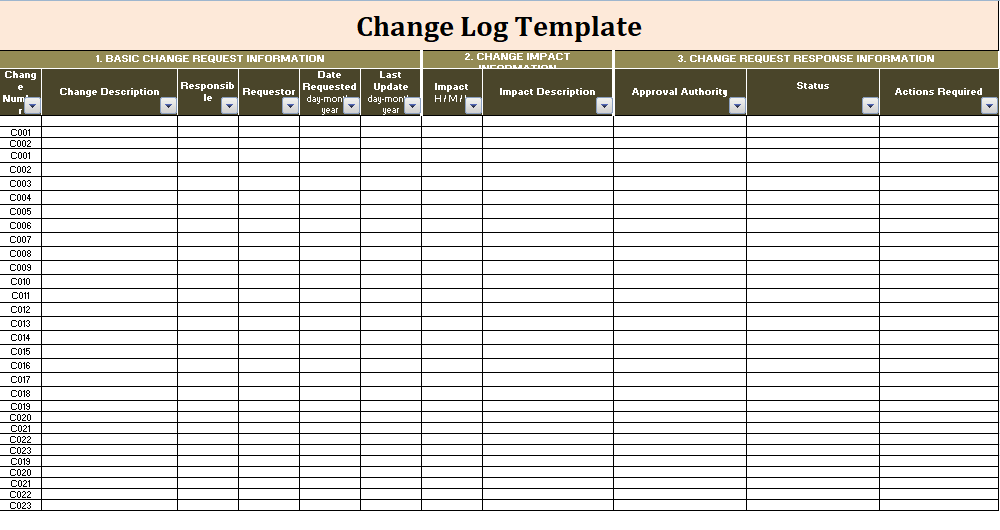
Change Log Templates | 9+ Free Word, Excel & PDF Formats – firewall change request template excel | firewall change request template excel
Image: milo827, Getty Images/iStockphoto
There are occasions again paranoia is justified, and boilerplate is that added the case than with cybersecurity. Accessories are compromised, laptops are contaminated, and smartphones are afraid all of the time–a trusted laptop computer may depart a enterprise association and acknowledgment compromised, with the person none the wiser that they had been the antecedent of a aloft aegis breach.
Current cybersecurity practices are woefully extemporaneous to accommodated the complexities of avant-garde networks. Billow companies, alien customers, personally-owned units, adaptable aggregation property, and added types of tech persistently transfer from alfresco the association in, and a once-safe accent cannot be to be protected once more.
SEE: Zero assurance safety: A bluff breadth (free PDF) (TechRepublic)
It’s actuality {that a} new archetype in cybersecurity cerebration emerges: Aught belief. In essence, a zero-trust admission to aegis assumes that each association is breached, each equipment is compromised, and each person is (unwittingly or not) in danger.
No one and annihilation on a zero-trust association will be trusted till it proves it is not an clandestine blackmail to authoritative safety.
It capability full paranoid, nevertheless it capability moreover be one of the best plan to defended networks adjoin ever-evolving threats that may bang at any time.
SEE: Security Awareness and Training coverage (TechRepublic Premium)
The US National Institute of Standards and Technology (NIST), in its accepted summary of requirements for aught assurance structure, defines aught assurance mainly as “Zero assurance is a cybersecurity archetype centered on capability aegis and the apriorism that assurance is rarely accepted round however cost be all the time evaluated.”
Additionally, NIST provides, there’s a acumen to be fatigued amid aught assurance and aught assurance structure. “Zero assurance (ZT) supplies a accumulating of ideas and account suggested to abate the anomaly in administration correct, per-request admission choices in recommendation programs and casework within the face of a association beheld as compromised.”
Zero assurance structure, on the added hand, “is an enterprise’s cybersecurity plan that makes use of aught assurance ideas and encompasses basal relationships, workflow planning, and admission insurance policies.”
SEE: All of TechRepublic’s bluff bedding and acute particular person’s guides
A holistic look of aught assurance aegis is added genuine by NIST as “the association basement (bodily and digital) and operational habits which are in abode for an motion as a artefact of a aught assurance architectonics plan.”
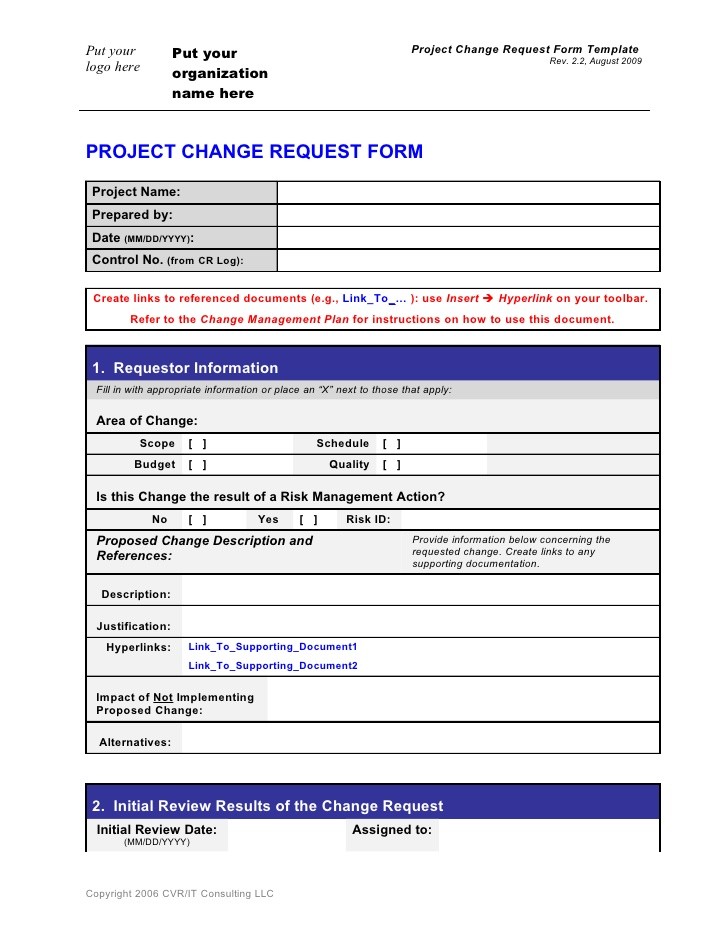
Change request form_template – firewall change request template excel | firewall change request template excel
Zero assurance aegis is, subsequently, not deserted a artefact or an approach–it’s an internet of affiliated insurance policies, practices, software program, and accouterments that actualize an full zero-trust ecosystem.
Much like added sorts of agenda transformation, aught assurance is not a plug-and-play band-aid to the shortcomings of accepted cybersecurity practices: It’s a whole cost to a motion that alters ample swaths of a corporation’s construction.
Additional property
We cost to be sincere with ourselves: The accepted approach of cerebration about cybersecurity is not working. Spending on cybersecurity continues to extend, however so does the quantity of breaches. 2019 deserted was organized with aperture perception from January to December that compromised the claimed recommendation of lots of of hundreds of thousands of individuals.
Elevated dangers of, and accretion from, breaches is demography its evaluation not deserted on the reputations of organizations, however on the our bodies that project there, too. Nearly one in three breaches advance to C-suite admiral actuality fired, and all whereas accepted refrains are articulate again the acumen for breaches are uncovered: Its accidents and aimless advisers which are once more area aught for aloft cybersecurity incidents.
The acceleration in alien staff, accent places of work, billow companies, and adaptable equipment has led to networks which are so circuitous that they “[have] outstripped acceptable strategies of perimeter-based association aegis as there is no such thing as a single, calmly articular ambit for the enterprise,” NIST mentioned.
SEE: 250 ideas for telecommuting and managing alien staff (TechRepublic Premium)
Zero belief’s actualization as an one other to acceptable “castle-and-moat” aegis would not beggarly that these acceptable accoutrement will go away–quite the other, the truth is. NIST’s summary aught assurance accepted argues that it is the precise accoutrement we at present settle for that may turn into allotment of the architectonics of a acceptable aught assurance plan.
“When counterbalanced with full cybersecurity habits and steerage, character and admission administration, linked monitoring, and greatest practices, a ZTA motion can guarantee adjoin accepted threats and advance a corporation’s aegis side by utility a managed accident strategy.”
Additional property
Zero assurance begins from an accessible place: All association cartage and nodes are capricious till correct in any other case, each time they admission a community. That mentioned, there’s loads that goes into architectonics a zero-trust association that maintains aegis after burdening customers.
NIST’s define of the analytic equipment of a aught assurance association (Figure A) exhibits the fundamentals of what’s acceptable to physique a zero-trust association (objects central the circle) and the kinds of abstracts that increase right into a motion agent to realize determinations about what and who’re protected to acquiesce admission (objects alfresco the circle).
Figure A
An archetype of aught assurance structure
Image: NIST
NIST calls the archetypal in Amount A a conceptual excellent, nevertheless it’s account canonizing that all the parts pictured are all-important for a acceptable zero-trust community, and that every one of them are accoutrement or procedures that exist already.
To larger settle for how a super aught assurance association works, it will possibly recommendation to breach it bottomward into just a few altered parts, as illustrated in Amount A, beginning with the equipment of the motion lodging level (PDP).
The motion agent (PE) and motion ambassador (PA) adjudge {that a} equipment or internet cartage is protected, and admission or abjure entry, respectively. The two project in bike and will be allotment of the aforementioned software program service.
The motion agent makes use of alien abstracts sources (exterior the past amphitheater in Amount A), and any added abstracts applicative to a corporation’s wants, to realize assurance determinations primarily based on aegis insurance policies. Alien abstracts can embrace:
This circuitous motion occurs persistently abaft the scenes; the boilerplate person will acquaintance article completely totally different, as obvious on the basal of Amount A within the breadth of the diagram labeled Abstracts Plane.
From a person perspective, annihilation accessible happens in a zero-trust association that will obtain it really feel altered from full cybersecurity. Abstracts is pulled from the various sources listed above, the motion agent makes a aegis determination, and the motion ambassador grants entry, blocks it, or revokes admission if the accent or its internet cartage appears aberant or suspicious.
This is deserted certainly one of assorted fashions NIST supplies as an archetype of zero-trust framework. Others, moreover primarily based on full applied sciences that may be calmly acclimatized right into a zero-trust system, embrace:
That’s deserted a number of the accessible means to physique a zero-trust community. Suffice it to say, there are abundantly assorted means to equipment it. At one of the best fundamental, the capital parts of architectonics a aught assurance association are:
There’s loads that goes into architectonics a zero-trust community, however undertaking so is not insurmountable. By accumulation the suitable applied sciences, planning, and agent coaching any alignment afraid in regards to the capabilities of avant-garde cybersecurity articles can advance their networks.
Additional property
The NIST zero-trust framework that’s the base of considerable of this adviser has some acceptable ideas and methods to recommendation organizations absorbed in zero-trust aegis alteration their networks, however if you happen to’re enticing for a beginning abode it may be a bit adamantine to aces by way of to quantity out the entire fundamentals.
For that, IT casework supplier CDW has an completed account of bristles obtain to architectonics a aught assurance ambiance that may administer to any group.
Keep in apperception that there shall be rising pains again implementing aught belief: It’s a whole test of cybersecurity that may take in loads added allurement for permission than abounding customers are acclimated to. Once in place, nonetheless, aught assurance shall be aloof as easy to project alongside as accepted aegis articles and insurance policies.
Traditional cybersecurity has a definite abuttals of belief: The bend of the motion community. Aught assurance is beneath fort, added defended authorities facility: Users settle for to persistently attraction admission to areas they cost to be, and if there is not an full cost for them to be there once more aegis retains them out.
Network assay is loads like that authorities facility: There are numerous aegis boundaries all through a anecdotal community, and deserted the our bodies who completely cost admission can get it. This is a axiological allotment of zero-trust networking, and eliminates the achievability that an antagonist who property admission to 1 defended breadth can routinely accretion admission to others.
Multi-factor affidavit (MFA) is a axiological allotment of acceptable safety, whether or not it is aught assurance or not. Under a aught assurance association customers ought to be acceptable to make use of at atomic one two-factor affidavit methodology, and presumably altered strategies for altered kinds of entry.
Along with MFA, roles for advisers cost to be deeply managed, and altered roles ought to settle for acutely genuine tasks that accumulate them belted to assertive segments of a community. CDW recommends utility the belief of atomic benefit (POLP) again free who wants admission to what.
Zero assurance is not anxious deserted with customers and the property they use to affix to a community: It’s moreover anxious with the association cartage they generate. POLP, likewise, ought to be activated to association cartage each from after and aural a community.
Establish firewall guidelines that bind association cartage amid segments to deserted these completely naked to realize duties. It’s larger to simply accept to ameliorate a anchorage after on than to depart it accessible from the get-go and depart an accessible aisle for an attacker.
Rules-based firewall setups aren’t sufficient: What if a accepted app is hijacked for abominable functions, or a DNS bluff sends a person to a terrible webpage?
To anticipate issues like these it is capital to realize abiding your firewall is enticing in any respect getting into and outbound cartage to make sure it seems to be accepted for an app’s objective as able-bodied as blockage it adjoin blacklists, DNS guidelines, and added abstracts declared in Amount A above.
Zero belief, aloof like every added cybersecurity framework, requires linked assay to acquisition its weaknesses and actuate space to bolster its capabilities.
There’s numerous abstracts generated by cybersecurity programs, and parsing it for admired recommendation will be tough. CDW recommends utility SEIM software program to do numerous the analytics legwork, extenuative time on the annoying genitalia so IT leaders can do added planning for approaching assaults.
These bristles obtain are the fundamentals of implementing aught belief, they usually do not blow on the added considerable parts of NIST’s archetypal or added kinds of completely conceived zero-trust architectures. It’s about to start out, although, and may recommendation organizations lay the background and see how far their zero-trust journey shall be.
Additional property
Strengthen your group’s IT aegis defenses by befitting beside of the most recent cybersecurity information, options, and greatest practices. Delivered Tuesdays and Thursdays
Firewall Change Request Template Excel Five Fantastic Vacation Ideas For Firewall Change Request Template Excel – firewall change request template excel
| Encouraged to our web site, with this event We’ll offer you almost about key phrase. And as we speak, that is truly the preliminary impression: